Email marketing is an effective and affordable digital marketing channel. If you’re running an e-commerce business, it’s a channel you should look into. Besides marketing […]
Think Long Term When It Comes to Protecting Your Precious Bike
You worked hard, and now the bike of your dreams is in your backyard. You can go on various road trips from mountains in the […]
Why Customer Success is Crucial for SaaS Companies
Customer Success (CS) is the company’s long-term strategy to make every client happy and satisfied. Still, the fact that you should take care of your […]
Paperless HR Solutions for Your Small Business
Managing payroll and human resource as a small business owner can be hard, as you hire someone, there are so many things that you need […]
Worx Lawn Mower
Worx Lawn Mower Worx Lawn Mower – Worx WG775 is a cordless electric lawn mower. It is not gas-powered, so there is no need to […]
What To Know When Choosing CRM Software for Your Small Business
Small Business CRM – Customer Relationship Management – Landing Page in Doodle design style on Laptop Screen. On background of Comfortable Working Place in Modern […]
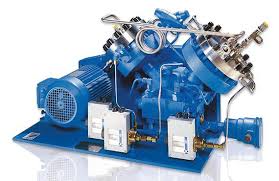
What Is A Diaphragm Compressor? How Does It Work?
Compressors are devices used for storage of atmospheric air in a high potential-used for pneumatic instruments. Diaphragm compressor is also called membrane compressor which compresses […]
How CBD Can Help Treat Your Insomnia
Did you know that “Almost 80 percent of Americans say they have trouble sleeping at least once a week? “ But this phenomenon is not […]
Top Personal Finance Mistakes Made By Couples And How To Fix Them By Ladder Advisors
Introduction Are you a newly married couple, trying to get your personal finances in order? As a couple, have you been experiencing problems related to […]
Accumulator betting: explained with examples
Accumulator bet, a.k.a accas, is currently one of the most popular forms of betting among fans of many sports, especially football enthusiasts. This gambling way […]